
Categories: All

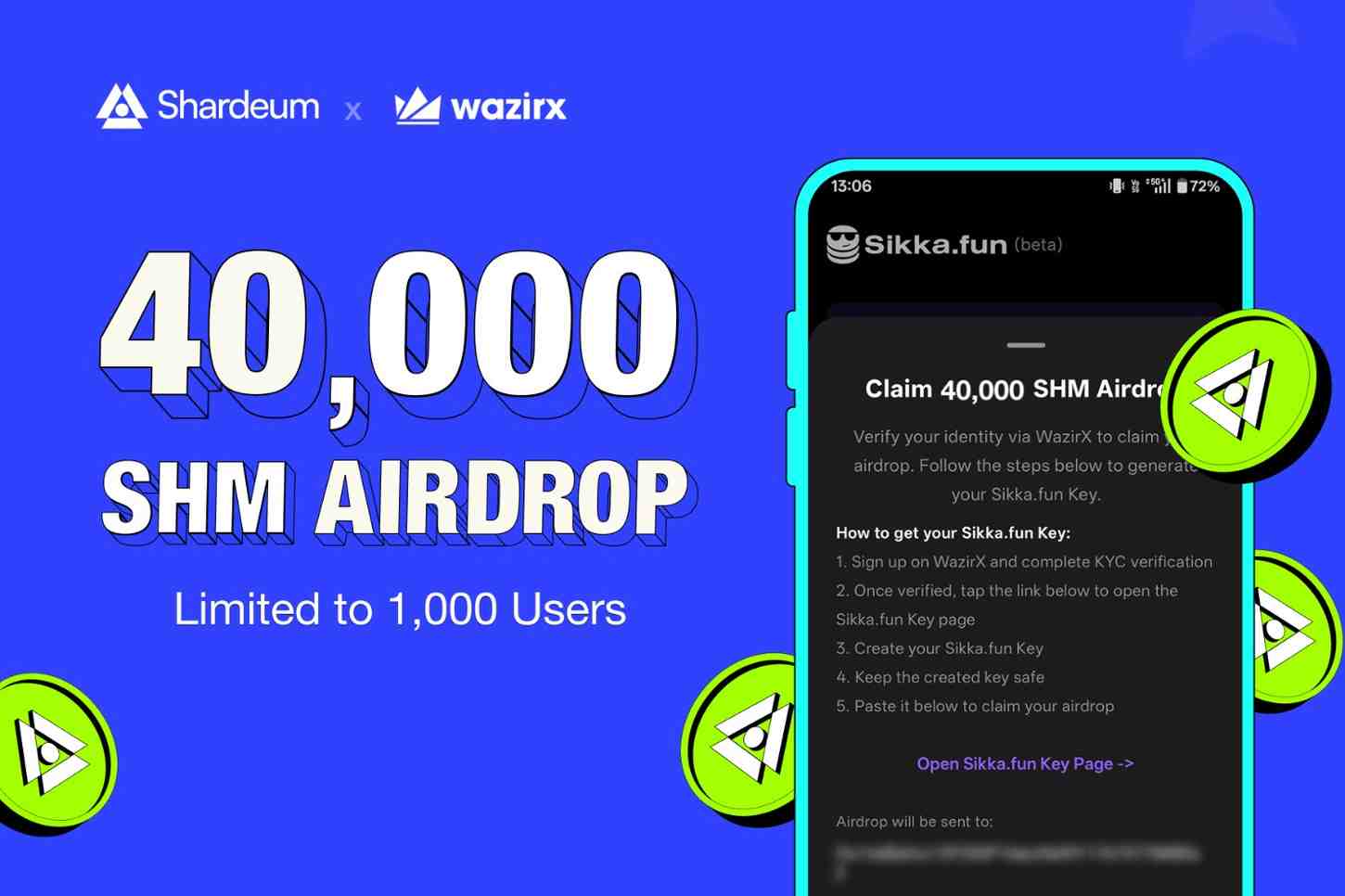
WazirX Phase 6 SHM airdrop is live. The first 1000 eligible users can claim 40,000 SHM each on Sikka.fun to start creating, trading, and earning...
Written By
WazirX Phase 5 SHM airdrop is live. The first 1000 eligible users can claim 25,000 SHM each on Sikka.fun to start creating, trading, and earning...
Written By
Explore Shardeum's key marketing metrics and growth highlights for April 2026, including community stats, engagement data, and campaign...
Written By
Discover CHIP, a social game built on Shardeum. Answer simple questions, estimate crowd behavior, and earn rewards based on your...
Written By
WazirX users with at least 1 WRX can claim 25,000 SHM on Sikka.fun. Limited to the first 1000 users. Start creating, trading, and earning in minutes....
Written By
Explore Shardeum's key marketing metrics and growth highlights for March 2026, including community stats, engagement data, and campaign...
Written By
Sikka.fun is now available in Indonesia, Nigeria, Vietnam, and Ukraine. Explore the latest app updates including trade volume discovery and INR/USD...
Written By
HackSprint brought together 200+ builders to create 110 real-world projects on Shardeum in 3 days. Explore key highlights, top builds, and...
Written By
WazirX users can claim 25,000 SHM on Sikka.fun (Phase 3). Limited to 1000 users holding 5000+ WRX. Create and trade coins in...
Written By
WazirX users can claim 50,000 SHM on Sikka.fun. Limited to the first 1,000 users. Get started with coin creation and trading in...
Written By
Explore Shardeum's key marketing metrics and growth highlights for February 2026, including community stats, engagement data, and campaign...
Written By
Sikka.fun is now live on Shardeum. Create your own coin, trade using a fair-launch bonding curve model, and earn through coin...
Written By
SHM trading is officially live on WazirX in the SHM/USDT market, accompanied by a 52.9M SHM “Highest Trader Kaun” contest from Feb 25 - Mar...
Written By
470+ Proof of Community events
28,000 Attendees
22 Countries
470+ Proof of Community events
28,000 Attendees
22 Countries
470+ Proof of Community events
28,000 Attendees
22 Countries
470+ Proof of Community events
28,000 Attendees
22 Countries


Learn how to delegate SHM on Shardeum, choose reliable validators, and earn staking rewards. A step-by-step guide for beginners and existing...
Written By
Buy SHM from exchanges and easily add it to your Shardeum wallet. Follow this quick guide to fund your wallet and start using SHM on the...
Written By
Learn how to set up your Shardeum wallet and connect to the mainnet in minutes. Start using SHM on a network built for ultra-low fees and limitless...
Written By
